In order to federate with your Active Directory with our services, contact technical support and then follow these instructions when directed:
On your ADFS farm you will need to follow these steps:
Add the RP trust
- In Server Manager, click Tools, and then select AD FS Management.
- In the console tree, under AD FS, right click Relying Party Trusts. Select Add Relying Party Trust.
- Select Claims Aware and click Start.
- On the Select Data Source page, select the option "Import data about the claims provider published online or on a local network". Enter the URI of our federation metadata endpoint:
https://login.mgcld.com/federationmetadata/2007-06/federationmetadata.xml
- On the Specify Display Name page, enter a name (e.g. MGCLD)
- On the Choose Access Control Policy page, choose a policy. You could permit everyone in the organization, or choose a specific security group.
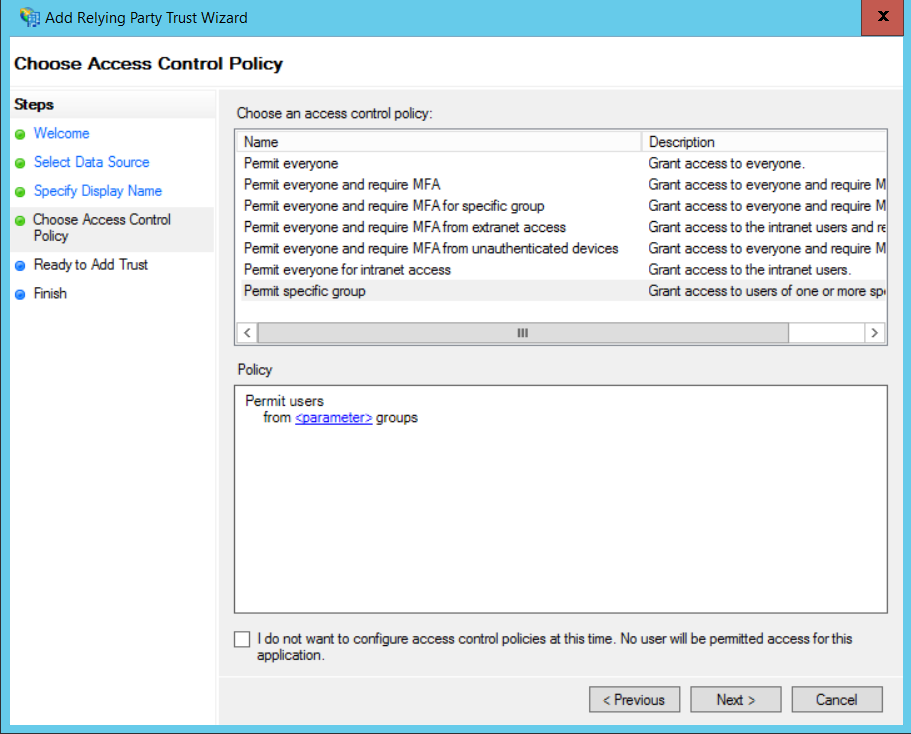
- Enter any parameters required in the Policy box.
- Click Next to complete the wizard.
Add claims rules
-
Right-click the newly added relying party trust, and select Edit Claim Issuance Policy.
-
Click Add Rule.
-
Select "Send LDAP Attributes as Claims" and click Next.
-
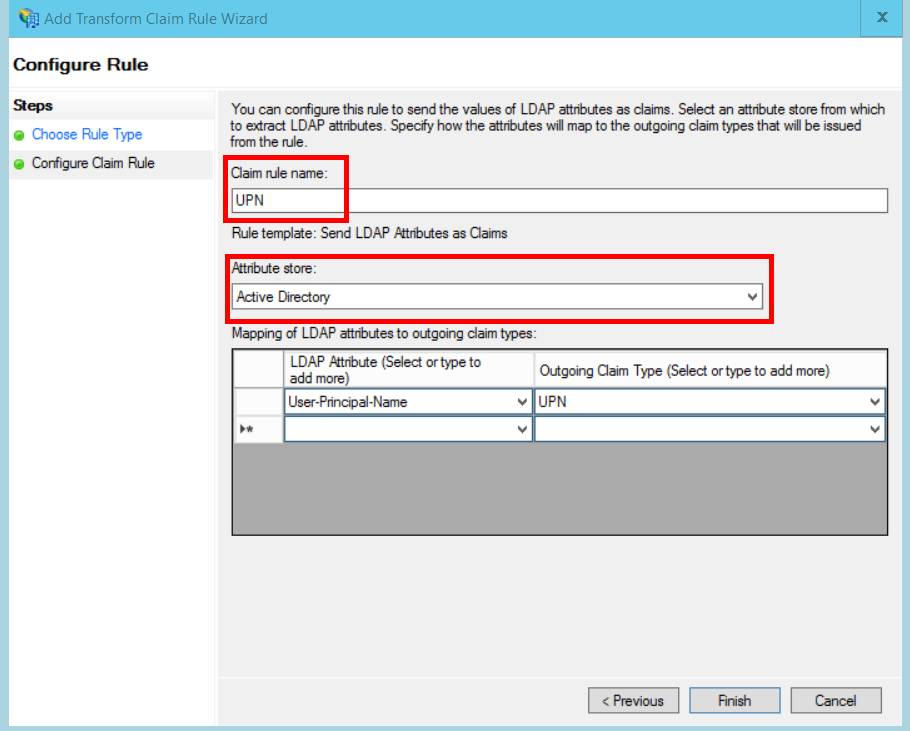
Enter a name for the rule, such as "Send LDAP UPN".
-
Under Attribute store, select Active Directory.
-
In the Mapping of LDAP attributes section:
- Under LDAP Attribute, select User-Principal-Name.
- Under Outgoing Claim Type, select UPN.

-
Click Finish.
-
Click Add Rule again.
-
Select "Send Claims Using a Custom Rule" and click Next.
-
Enter a name for the rule, such as "Anchor Claim Type".
-
Under Custom rule, enter the following:
EXISTS([Type == "http://schemas.microsoft.com/ws/2014/01/identity/claims/anchorclaimtype"])=> issue (Type = "http://schemas.microsoft.com/ws/2014/01/identity/claims/anchorclaimtype", Value = "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn");
This rule issues a claim of type anchorclaimtype. The claim tells the relying party to use UPN as the user's immutable ID. -
Click Finish.
-
Click OK to complete the wizard.
Comments
0 comments
Please sign in to leave a comment.